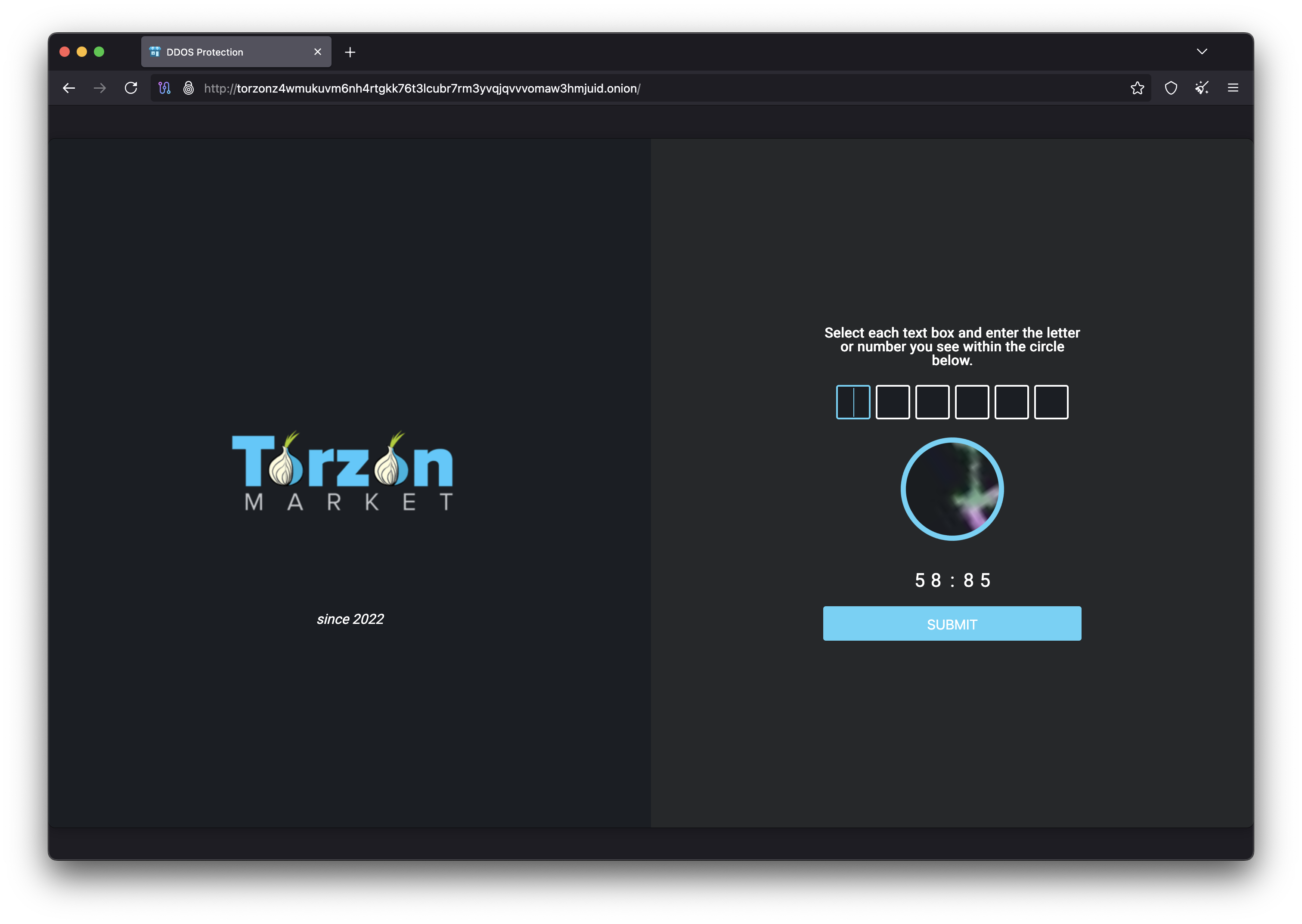
Torzon Market Access Guide
How to Access Torzon Safely in 2026
This comprehensive guide explains how to access Torzon Market safely and securely. Learn about Tor Browser configuration, secure operating systems like Tails and Whonix, identity protection, and operational security best practices for accessing Torzon Market. Following these guidelines ensures your privacy when using Torzon.
Accessing Torzon Market Safely
Torzon Market is a darknet marketplace accessible only through the Tor network. To access Torzon safely, you must use specialized software and follow strict operational security (OPSEC) practices. This guide covers everything you need to know about connecting to Torzon Market while protecting your privacy and security.
The Torzon Market team strongly emphasizes user security and provides guidelines for safe access. Following these recommendations protects you from common threats including surveillance, phishing attacks, and identity exposure. Never take shortcuts when accessing Torzon - proper OPSEC is essential.
Tor Browser for Torzon
Essential configuration for accessing Torzon Market
All access to Torzon Market requires the Tor Browser. The Tor Browser Bundle provides a pre-configured Firefox browser that routes all traffic through the Tor network, enabling access to .onion sites like Torzon. Never attempt to access Torzon through regular browsers like Chrome, Firefox, or Edge.
Downloading Tor Browser for Torzon Access
Download Tor Browser only from the official website: torproject.org. Verify the download signature before installation. Phishing sites distributing modified Tor Browser versions are common threats - a compromised browser could expose your Torzon activity.
Tor Browser Security Settings for Torzon
When accessing Torzon Market, configure Tor Browser to the "Safest" security level:
- Open Tor Browser Settings
- Navigate to Privacy & Security
- Set Security Level to "Safest"
The Safest setting disables JavaScript by default, eliminating entire categories of deanonymization attacks when browsing Torzon. This includes browser fingerprinting, WebRTC leaks, and exploit delivery through malicious scripts. Torzon Market functions fully without JavaScript.
Secure Operating Systems for Torzon
Tails and Whonix provide enhanced security for Torzon Market access
While Tor Browser provides basic anonymity, accessing Torzon Market from your daily operating system (Windows, macOS, standard Linux) introduces risks. These systems contain telemetry, potential malware, and configuration that could leak identifying information. For maximum security when using Torzon, use a dedicated secure operating system.
Tails OS for Torzon
The Amnesic Incognito Live System
Tails runs from USB with no installation required. All traffic routes through Tor automatically, making it ideal for Torzon access. Tails leaves no traces on the host computer - complete amnesia on shutdown. Includes pre-configured security tools (PGP, encrypted storage).
Best for: Torzon users who want maximum privacy with minimal configuration.
Whonix for Torzon
Security Through Isolation
Whonix uses a two-VM architecture separating the Tor gateway from the workstation. This design makes it impossible for malware on the workstation to leak your IP when accessing Torzon. Even if compromised, the workstation cannot bypass the Tor gateway.
Best for: Advanced Torzon users requiring persistent storage and installed software.
Tails vs Whonix for Torzon Access
| Feature | Tails (Torzon) | Whonix (Torzon) | Qubes + Whonix |
|---|---|---|---|
| Difficulty | Easy | Moderate | Advanced |
| Torzon Data Persistence | Optional encrypted | Full | Full |
| Tor Bypass Risk | Very Low | Zero | Zero |
| Forensic Resistance | Excellent | Moderate | Excellent |
| Torzon Recommendation | Beginners | Intermediate | Maximum Security |
Torzon Identity Protection
Maintaining anonymity while using Torzon Market
Technical security measures become worthless if you voluntarily provide identifying information on Torzon Market. Strict identity compartmentalization ensures your Torzon activities cannot be linked to your real-world identity through information correlation.
Information Hygiene on Torzon
- Never use real names, emails, or phone numbers on Torzon: Even partial information enables correlation attacks that could identify you.
- Create unique Torzon credentials: Your Torzon username and password must not match any other accounts you own.
- Avoid personal details in Torzon communications: Writing style, timezone references, and local knowledge can leak your identity.
- Never cross-reference identities: Your Torzon activities must remain completely separate from clearnet life.
Behavioral OPSEC for Torzon
Beyond technical measures, behavioral patterns can identify Torzon users through stylometry (writing style analysis), timezone correlation, and activity patterns:
- Vary Torzon usage times: Consistent access patterns reveal your timezone.
- Never discuss Torzon activities: Not with anyone, under any circumstances.
- Be aware of writing style: Distinctive phrases enable stylometric analysis of Torzon communications.
- Manage metadata: Strip EXIF data and document properties before sharing files on Torzon.
Torzon PGP Communication
Encrypted messaging on Torzon Market
All sensitive communications on Torzon Market should use PGP encryption. PGP (Pretty Good Privacy) provides military-grade encryption that even Torzon administrators cannot decrypt. When sending sensitive information like shipping addresses, always encrypt with the recipient's PGP key.
Setting Up PGP for Torzon
- Generate PGP keys through Tor: Create your Torzon PGP keys while connected to Tor. Never reuse keys from clearnet activities.
- Use a pseudonym: Your Torzon PGP key should contain only your Torzon username, not real identifying information.
- Set appropriate key strength: Use RSA 4096-bit or equivalent for Torzon communications.
- Back up securely: Store your Torzon private key backup encrypted, separate from your Torzon-access device.
Torzon PGP Best Practices
- Encrypt all sensitive Torzon data: Addresses, personal information, and financial details must always be encrypted.
- Verify Torzon vendor keys: Confirm key fingerprints through secondary channels before sending sensitive information.
- Never send plaintext on Torzon: Assume all unencrypted Torzon communications are logged.
- Use Torzon's built-in PGP features: Torzon Market provides integrated PGP encryption for messages.
Torzon Device Security
Hardware requirements for safe Torzon access
Dedicated Hardware for Torzon
Torzon Market strongly recommends using dedicated hardware for darknet activities. Never use your daily-use devices to access Torzon. A separate device prevents cross-contamination between your Torzon identity and regular activities.
Ideal Torzon hardware configuration:
- Separate laptop: Used exclusively for Torzon access
- Full disk encryption: Strong passphrase protecting all Torzon data
- BIOS password: Prevents unauthorized boot modification
- Physical security: Secured storage when not accessing Torzon
Mobile Device Warning for Torzon
Torzon Market officially discourages mobile access. Mobile devices present unacceptable security risks due to numerous identifier leakage vectors:
Mobile risks for Torzon access include: IMEI/IMSI hardware identifiers, GPS location services, cell tower triangulation, advertising IDs, app permissions, and reduced Tor Browser security. Use desktop/laptop systems for Torzon.
Torzon OPSEC Checklist
Verify before each Torzon Market session
Tor & Access Security Videos
Learn about Tor hidden services, PGP encryption, and privacy-focused operating systems.
Tor Hidden Services
PGP Encryption Tutorial
Linux Privacy and Security
Continue Learning About Torzon
Explore more Torzon Market guides