Torzon Market Security
Advanced Cryptographic Protection & Zero-Knowledge Architecture
Torzon Market implements industry-leading security technologies to protect user privacy and funds. This comprehensive analysis covers Torzon's post-quantum cryptography, zero-knowledge infrastructure, multi-layer authentication, and advanced threat protection mechanisms that make Torzon one of the most secure darknet marketplaces in 2026.
Torzon Market Security Overview
Torzon Market has established a reputation for security excellence in the darknet marketplace ecosystem. The Torzon security architecture incorporates multiple defensive layers, from post-quantum cryptography protecting communications to RAM-only servers ensuring no persistent data storage. Understanding Torzon Market's security measures helps users make informed decisions about their privacy and fund protection.
The Torzon Market development team has prioritized security from the platform's inception, implementing features that remain rare among darknet marketplaces. Torzon's approach to security goes beyond basic encryption, incorporating advanced concepts from academic cryptography and operational security research. This document provides a detailed technical analysis of Torzon Market's security architecture.
Torzon Post-Quantum Cryptography
Future-proof encryption protecting Torzon Market against quantum computing threats
Torzon Market stands among the first darknet marketplaces to implement post-quantum cryptographic standards. While traditional encryption methods like RSA and ECC remain secure against current computers, quantum computers running Shor's algorithm could break these systems within the next 10-20 years. Torzon's proactive implementation of quantum-resistant cryptography addresses this emerging threat.
The Torzon Market platform implements NIST-approved lattice-based algorithms, likely including CRYSTALS-Kyber for key encapsulation and CRYSTALS-Dilithium for digital signatures. These algorithms derive their security from the mathematical hardness of lattice problems, which remain computationally infeasible even for quantum computers.
Why Torzon Implemented Post-Quantum Security
The primary motivation for Torzon Market's quantum-resistant encryption is the "store now, decrypt later" attack vector. Adversaries can intercept and store encrypted Torzon communications today, then decrypt them once sufficiently powerful quantum computers become available. For users of Torzon Market, where communications may contain sensitive information, this represents a serious long-term threat.
By implementing post-quantum cryptography now, Torzon ensures that all platform communications remain confidential indefinitely. Torzon Market users benefit from this protection without any additional configuration - the security is built into the platform infrastructure.
Torzon Zero-Knowledge Architecture
RAM-only infrastructure ensuring no persistent data storage on Torzon servers
Torzon Market operates on a zero-knowledge architecture with RAM-only servers that contain no persistent storage devices. This stateless design represents a fundamental security improvement over traditional marketplace architectures. When Torzon servers are powered down or rebooted, all data in memory is permanently erased.
Torzon Market Data Retention Policies
The Torzon Market platform enforces strict data minimization policies:
- Transaction Records: Torzon purges after 14 days maximum
- Access Logs: Torzon erases within 12 hours
- IP Addresses: Never written to disk on Torzon servers
- Message Contents: Deleted after 30 days on Torzon
These aggressive data retention policies ensure that even if Torzon Market servers were seized by law enforcement, minimal useful information would be available. The RAM-only architecture means that powering down servers immediately destroys all data.
Benefits of Torzon's RAM-Only Design
The Torzon Market zero-knowledge infrastructure provides several critical security benefits:
Physical Seizure Protection
If law enforcement physically seizes Torzon servers, they obtain no usable data. RAM contents are lost immediately upon power interruption. Torzon's architecture ensures physical access provides no intelligence advantage.
Forensic Analysis Mitigation
Traditional digital forensics techniques are ineffective against Torzon's RAM-only servers. Without persistent storage, there are no disk images to analyze, no deleted files to recover, and no historical data to examine.
Automatic Data Minimization
Torzon Market's architecture enforces privacy-by-design principles. The platform cannot retain data longer than technically necessary. This protects Torzon users even from potential future policy changes.
Cold Boot Attack Resistance
Torzon implements RAM encryption to protect against sophisticated cold boot attacks that attempt to recover memory contents. Even physical access to running Torzon servers provides minimal recoverable information.
Torzon Authentication Security
Multi-layer authentication options protecting Torzon Market accounts
Torzon Market provides three distinct two-factor authentication (2FA) mechanisms, allowing users to choose their preferred security level. Torzon's authentication hierarchy progresses from standard TOTP support through authenticator apps, to PGP-based challenge-response, culminating in hardware security key support.
Torzon 2FA Options
TOTP Authentication
Torzon Market supports standard Time-based One-Time Passwords (TOTP) through authenticator apps like Aegis, andOTP, or KeePassXC. This provides basic 2FA protection for Torzon accounts using six-digit codes that change every 30 seconds.
Standard SecurityPGP Authentication
Torzon Market offers PGP-based challenge-response authentication. When logging into Torzon, users decrypt an encrypted challenge message with their private key. This provides stronger authentication than TOTP while ensuring cryptographic identity verification.
Enhanced SecurityHardware Keys
Torzon Market supports FIDO U2F hardware security keys like YubiKey and Google Titan. These devices provide phishing-resistant authentication for Torzon accounts, cryptographically verifying the domain to prevent credential theft through fake sites.
Maximum SecurityTorzon PGP Verified Vendor Import
Torzon Market features a unique PGP verified vendor import system that enables cryptographically verified reputation migration from other marketplaces. Vendors sign messages with their established PGP keys, which Torzon verifies against known public keys from platforms like ASAP, Dark0de Reborn, and former Archetyp vendors.
This Torzon feature enables trust transfer while preventing fraudulent reputation claims through strong cryptographic guarantees. New vendors on Torzon can establish credibility immediately if they have verifiable history on other platforms.
Torzon Warrant Canary System
Cryptographically signed transparency reports verifying Torzon Market integrity
Torzon Market maintains an active warrant canary system that is updated every 72 hours. A warrant canary is a transparency mechanism where the platform publishes regular signed statements confirming they have not received secret legal orders, such as National Security Letters or gag orders that would prevent disclosure.
Each Torzon warrant canary contains:
- Current Date: Proves when the Torzon canary was created
- Recent News Events: References to verifiable current events proving creation date
- PGP Signature: Cryptographic proof the canary came from Torzon administrators
- Statement of Non-Compromise: Explicit declaration that Torzon has not been served with secret orders
Torzon users should regularly verify the warrant canary to confirm platform integrity. If the canary stops being updated or its statements change, this signals potential compromise of Torzon Market. The 72-hour update cycle provides timely notification of any issues.
Torzon DDoS Protection
Multi-layer infrastructure protecting Torzon Market availability
Torzon Market maintains robust DDoS protection infrastructure ensuring platform availability even under attack. The Torzon network architecture includes multiple mirror sites, load balancing, and traffic filtering to mitigate denial-of-service attempts.
Torzon Mirror Infrastructure
Torzon operates 9+ mirror sites distributed across different Tor circuits and hosting locations. This redundancy ensures that if individual Torzon mirrors are attacked or taken offline, users can access the platform through alternative links. Each Torzon mirror provides identical functionality.
Torzon Traffic Analysis Protection
The Torzon Market architecture includes measures to prevent traffic analysis attacks that could correlate user behavior across sessions. Torzon implements uniform response timing, traffic padding, and other techniques to minimize information leakage through network timing channels.
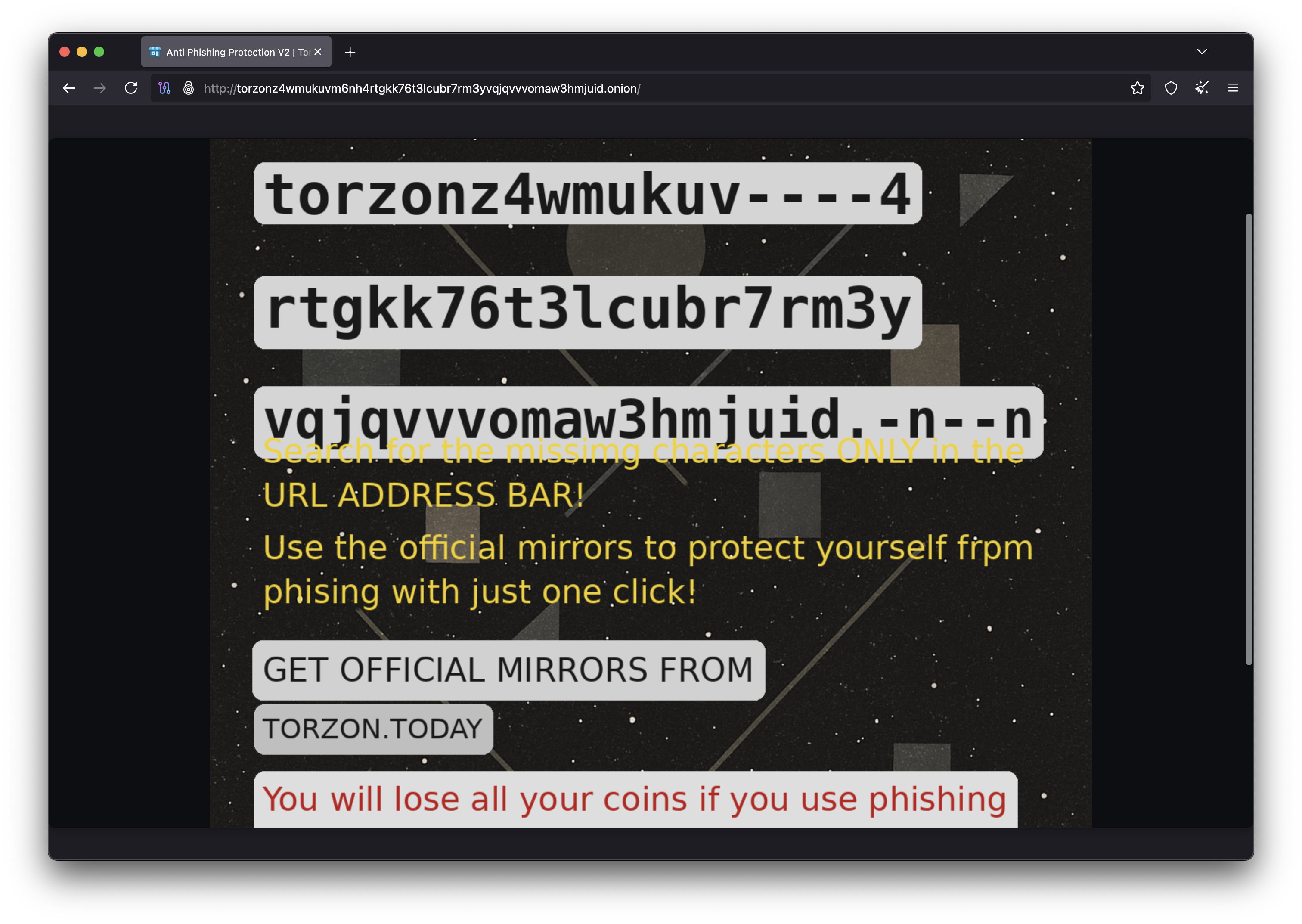
Torzon Anti-Phishing Protection
Security features helping Torzon users avoid fraudulent sites
How Torzon Anti-Phishing Works
When you create a Torzon Market account, you set a unique security phrase that only you and Torzon know. This phrase is displayed on every login page. Phishing sites cannot display your correct phrase because they don't have access to Torzon's database.
Always verify your Torzon security phrase before entering your password. If the phrase is missing, incorrect, or generic, you may be on a phishing site attempting to steal your Torzon credentials.
Torzon Security Comparison
How Torzon Market security compares to industry standards
| Security Feature | Torzon Market | Industry Standard | Assessment |
|---|---|---|---|
| Post-Quantum Cryptography | NIST Lattice-Based | Classical RSA/ECC | Torzon Leads |
| Server Architecture | RAM-Only (Torzon) | Persistent SSD | Torzon Superior |
| Warrant Canary | 72-Hour (Torzon) | Not Implemented | Torzon Unique |
| 2FA Options | TOTP + PGP + Hardware | TOTP Only | Torzon Complete |
| Anti-Phishing | Security Phrase | Basic/None | Torzon Protected |
Torzon Market Security Best Practices for Users
While Torzon Market implements advanced security infrastructure, user security depends equally on operational security (OPSEC) practices. Torzon provides the platform security, but users must secure their connection and protect their identities. This section covers essential security practices for Torzon Market users.
Essential Security Measures for Torzon Access
Accessing Torzon Market securely requires using Tor Browser with proper security settings. Torzon Market is a hidden service accessible only through the Tor network, which provides anonymity by routing traffic through multiple encrypted nodes. Never attempt to access Torzon through regular browsers like Chrome or Firefox as this compromises anonymity and may expose your IP address.
Configure Tor Browser security settings to "Safest" when accessing Torzon Market. This disables JavaScript on Torzon and other potentially dangerous features that could compromise anonymity. While Torzon Market functions without JavaScript, some interactive features may be limited. Prioritize security over convenience when using Torzon.
Torzon Market Operating System Security
For maximum security when accessing Torzon Market, use a secure operating system designed for privacy. Tails OS is the gold standard for Torzon access - it's a live operating system that routes all traffic through Tor, leaves no traces on the host computer, and includes built-in privacy tools. Torzon users can run Tails from a USB drive without installing anything on their computer.
Whonix provides an alternative secure environment for Torzon Market access through a two-virtual-machine architecture. The Whonix-Gateway VM handles all Tor connections while Whonix-Workstation accesses Torzon Market. This isolation ensures that even if malware infects the Torzon workstation, it cannot discover your real IP address.
Torzon Account Security Recommendations
Creating a secure Torzon Market account starts with a strong, unique password. Use a password manager like KeePassXC to generate and store a random password specifically for Torzon. Never reuse passwords from other services on Torzon Market. If another service is breached, attackers could use credential stuffing to access your Torzon account.
Enable two-factor authentication immediately after creating your Torzon account. Torzon Market supports TOTP, PGP, and hardware security keys. Hardware keys provide the strongest protection for Torzon accounts, offering phishing-resistant authentication that verifies you're accessing the authentic Torzon Market site. PGP authentication provides strong cryptographic identity verification for Torzon users comfortable with encryption.
Torzon Market Communication Security
All sensitive communication on Torzon Market should be encrypted with PGP. Torzon provides PGP integration for vendor communications, but users must generate and manage their own PGP keys. Generate PGP keys on the same secure system you use for Torzon access - preferably Tails or Whonix. Never generate Torzon-related PGP keys on Windows or macOS without full-disk encryption.
When communicating with vendors on Torzon Market, always encrypt your shipping address and sensitive information. Torzon's infrastructure security cannot protect unencrypted messages if the platform is compromised. End-to-end PGP encryption ensures that only you and your Torzon vendor can read message contents.
Torzon Market Financial Security
Cryptocurrency security is crucial for Torzon Market users. Torzon accepts Bitcoin, Monero, and Litecoin, but security practices differ significantly between cryptocurrencies. Monero provides protocol-level privacy features making it Torzon's recommended currency. Bitcoin requires additional privacy measures when using Torzon to prevent transaction analysis.
For Bitcoin users on Torzon Market, use CoinJoin mixing services like Wasabi Wallet before depositing to Torzon. This breaks the transaction chain linking your identity to Torzon deposits. Never deposit Bitcoin directly from an exchange to Torzon Market - exchanges monitor withdrawal addresses and could flag Torzon-linked accounts. Monero users have fewer concerns as Torzon transactions are private by default through ring signatures and stealth addresses.
Only deposit cryptocurrency you're ready to spend on Torzon Market. While Torzon implements multi-signature escrow and cold storage security, no darknet marketplace is completely safe from exit scams or law enforcement seizure. Minimize Torzon wallet balances and withdraw funds promptly after successful transactions complete.
Torzon Market Phishing Prevention
Phishing sites impersonating Torzon Market represent a serious threat. Attackers create fake Torzon sites to steal login credentials and cryptocurrency deposits. Always verify Torzon Market links through PGP signature verification before accessing. The official Torzon PGP key should be obtained from multiple independent sources and used to verify all mirror lists.
Bookmark verified Torzon Market links in Tor Browser to avoid needing to search for links each time. Never access Torzon through clearnet search engines, forums, or shortened links. These are common phishing vectors where attackers promote fake Torzon sites. Check your anti-phishing security phrase on every Torzon login - if it's missing or incorrect, you're on a phishing site.
Torzon Market Vendor Security Verification
Torzon Market's security infrastructure protects the platform, but users must still verify vendor legitimacy. Torzon implements vendor bond requirements and reputation systems, but new vendors or those without established history require extra scrutiny. Check vendor PGP keys on Torzon and verify they match keys published on other platforms or trusted directories.
Review Torzon vendor feedback carefully, looking for detailed reviews with specific transaction information rather than generic praise. Scammers often create fake Torzon accounts with manufactured positive feedback. Start with small orders when trying new vendors on Torzon Market to limit potential losses from scams. Torzon's escrow system protects against non-delivery, but quality issues may be harder to resolve.
Torzon Market Security Incident Response
If you suspect your Torzon Market account has been compromised, immediately change your password and regenerate your 2FA secret. Withdraw any remaining funds from your Torzon wallet to a secure external address. Review your Torzon order history and messages for unauthorized activity. Contact Torzon support if you notice suspicious transactions or account changes you didn't initiate.
If Torzon Market's warrant canary expires or changes unexpectedly, consider this a potential platform compromise. Stop accessing Torzon and monitor community discussions about the platform's status. Do not deposit additional funds to Torzon until the situation is clarified. The warrant canary system exists specifically to provide early warning of Torzon security issues.
Torzon Market Security FAQs
Common questions about Torzon security answered
How does Torzon Market protect against exit scams?
Torzon Market uses 2-of-3 multi-signature escrow with time-locked contracts. Unlike traditional escrow where Torzon holds funds directly, the multi-sig system requires two of three parties (buyer, vendor, Torzon) to sign releases. Time-locks automatically return funds to buyers after 14 days if disputes remain unresolved. This means Torzon administrators cannot steal escrowed funds even if they wanted to execute an exit scam.
Can law enforcement compromise Torzon Market's RAM-only servers?
Torzon's RAM-only architecture makes traditional server seizures largely ineffective. When Torzon servers lose power, all data in RAM is immediately erased. Law enforcement would need to maintain continuous power to the servers and have specialized memory forensics tools ready at the moment of seizure. Even then, Torzon implements RAM encryption making memory extraction extremely difficult. Physical server compromise provides minimal intelligence about Torzon users.
Why does Torzon Market need post-quantum cryptography now?
Torzon implements post-quantum cryptography to protect against "store now, decrypt later" attacks. Even though quantum computers cannot break current encryption today, adversaries can intercept and archive encrypted Torzon communications now, then decrypt them when quantum computers become available (estimated 10-20 years). For Torzon users discussing sensitive transactions, this future decryption represents a serious threat that post-quantum encryption eliminates.
How does Torzon Market's warrant canary work?
Torzon publishes a cryptographically signed statement every 72 hours declaring the platform has not been compromised or served with secret legal orders. Each Torzon canary includes current date references and news events proving when it was created. If Torzon fails to update the canary or removes specific statements, this signals potential compromise. Users should verify the Torzon warrant canary signature using the platform's official PGP key before each session.
Is Torzon Market secure if I don't use Tails or Whonix?
Torzon Market's infrastructure security protects the platform, but your personal security depends on your operating system choices. While Torzon can be accessed from regular operating systems running Tor Browser, this provides less protection than Tails or Whonix. Windows and macOS have numerous privacy weaknesses that could compromise your identity even when using Torzon through Tor. For high-security Torzon operations, dedicated privacy operating systems are strongly recommended.
What makes Torzon Market's anti-phishing system effective?
Torzon's personal security phrase system defeats phishing attacks because fake sites cannot display your unique phrase. When you set up a Torzon account, you create a personalized security phrase stored in the platform's database. This phrase appears on every legitimate Torzon login page. Phishing sites don't have access to Torzon's database, so they either show no phrase, a generic phrase, or a random phrase - immediately alerting you that you're not on the authentic Torzon Market.
Encryption & Security Videos
Learn about advanced encryption, security architecture, and quantum computing threats.
End-to-End Encryption
AES Explained
Quantum Computing and Cryptography
Continue Learning About Torzon
Explore more Torzon Market guides and resources
Torzon Cryptocurrency
Learn about Bitcoin and Monero payments on Torzon Market, including escrow and wallet security.
Read GuideTorzon Access Guide
Step-by-step instructions for safely accessing Torzon Market through Tor Browser.
Read GuideTorzon Mirrors
Official verified Torzon Market mirror links with PGP verification guide.
View Mirrors